SCALYS for Government and Defense
Scalys is leader in cyber secure communications, serving government and defense bodies around the globe with great commitment to zero-trust and hardware security.
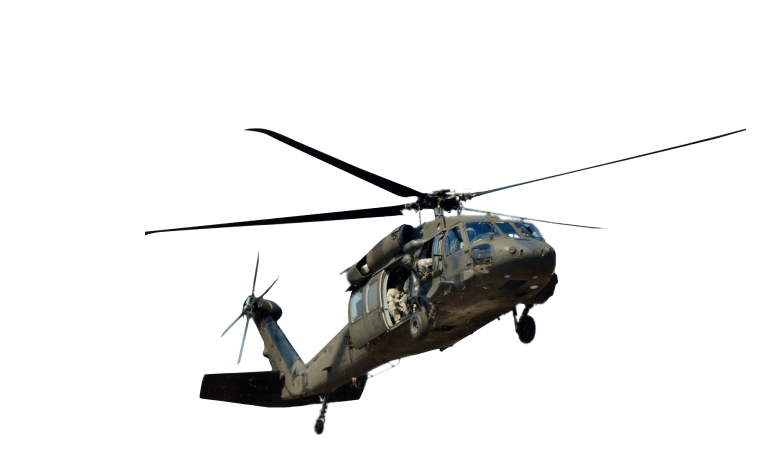
Remote working challenges
You work on a global level, and your staff requires constant access to your organization’s network. Yet, every interaction and data exchange made with their laptops demands the highest confidentiality. That is why no infrastructure except your organization’s internal network can guarantee proper security. How do you approach this challenge?
Revolutionizing Remote Operations: TrustBox Connect
Introducing the TrustBox Connect by Scalys, a solution designed to redefine secure remote working. Through hardware-enforced VPN connectivity with your organization’s network, the TrustBox Connect offers improved cyber security to remote working employees across the globe. Built on zero-trust principles, this solution enhances security through multifactor authentication (MFA), trusted platform module (TPM), and trusted boot mechanisms.

Office ecosystem solutions
Our mission is to offer a secure remote office environment, tailored to the precise demands of global operating government and defense organizations. These organizations are renowned for their tight security requirements and confidentiality. Scalys offers office ecosystem solutions, developed in tight collaboration with various government bodies. It allows professionals the freedom to work remotely strengthened by our extensive experience in developing cyber-secure electronics, and designed to conform with the highest usability and security standards.
Implementation and design
Scalys is a partner that helps conceptualize, design, and implement networking and communication solutions. With a deep understanding of both hardware and software, we evaluate potential threats within your infrastructure, offering guidance in the integration of security protocols.
Our approach follows these steps:
- Discovery
- Security assessment
- Design
- User products
- Solution
- Implementation
Tailored Solutions to Fulfill Your Needs
With our knowledge in both hardware and software, our team makes a comprehensive analysis of threats within your infrastructure. We engineer customized solutions using standard devices tailored precisely to the unique requirements of your project. Other noteworthy achievements include secure unidirectional data transfers and bespoke protocols, ensuring seamless protection. Scalys is a trusted partner in the world of cyber security, with a specialization in secure communications. Our tailored solutions reinforce communication security, offering a robust defense against a wide range of cyber threats.
Let us join forces to strengthen the future of your organization.
