SCALYS for Smart energy
Scalys leads the smart energy market with cyber-secure communications. Building on zero-trust principles and hardware security, we leave no room for compromise. Our multi-layered approach ensures a reliable digital environment, where no device or user is automatically trusted. You can count on Scalys to protect your critical data and keep the integrity of your smart energy systems.
Grid infrastructure vulnerabilities
Managing your energy infrastructure is becoming increasingly difficult with growing market demands. While using the latest monitoring and maintenance solutions offers convenience and transparency, it also introduces vulnerabilities. Being able to rely on these systems for operational efficiency and correct data is important. However, how secure are these invaluable data and systems? While “Red Button” solutions are always a possibility to keep unwanted guests out, they are also very detrimental to your operations. Are you aware of the vulnerability of your operational technology (OT) to potential compromises?
Let Scalys help.
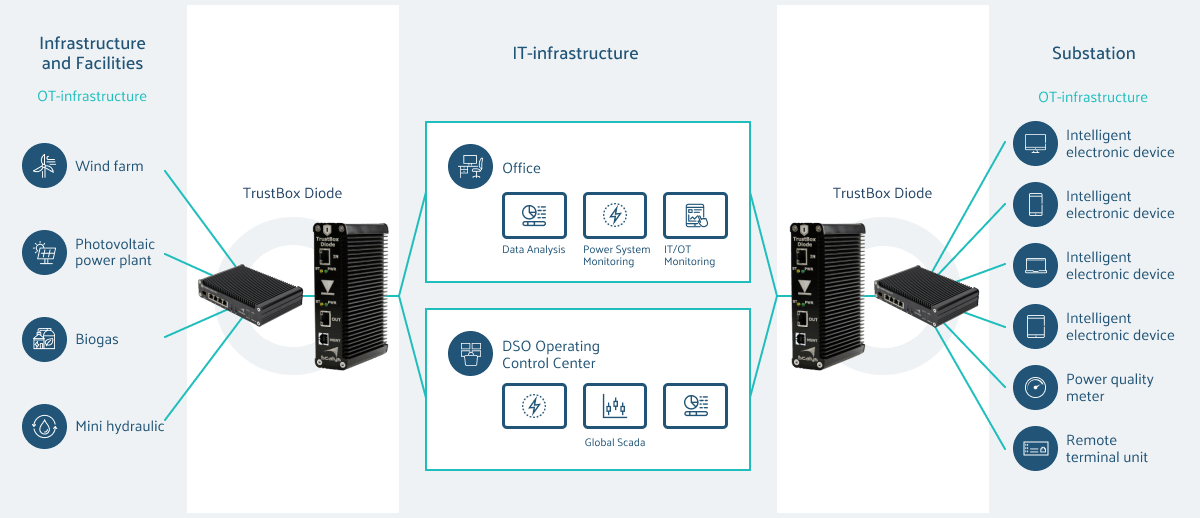
Improved grid protection: TrustBox Diode
With the TrustBox Diode Scalys offers a key security solution in the field of smart energy, providing protection by enabling one-way data transfer between operational technology (OT) and information technology (IT). The TrustBox Diodes’ implementation enhances reliability and security for Distribution System Operators (DSO) and Transmission System Operators (TSO) and strengthens Smart Remote Terminal Units (RTU) within the grid, minimizing tampering risks and improving data reliability in the middle of evolving energy market challenges.

Implementation and design
Scalys is a partner that helps conceptualize, design, and implement networking and communication solutions. With a deep understanding of both hardware and software, we evaluate potential threats within your infrastructure, offering guidance in the integration of security protocols.
Our approach follows these steps:
- Discovery
- Security assessment
- Design
- User products
- Solution
- Implementation

Tailor-made to YOUR needs
With our knowledge in both hardware and software, our team makes a comprehensive analysis of threats within your infrastructure. We engineer customized solutions using standard devices tailored precisely to the unique requirements of your project. Other noteworthy achievements include secure unidirectional data transfers and bespoke protocols, ensuring seamless protection. Scalys is a trusted partner in the world of cyber security, with a specialization in grid protection. Our tailored solutions reinforce communication security, offering a robust defense against a wide range of cyber threats.
Let us join forces to strengthen the future of your organization.
